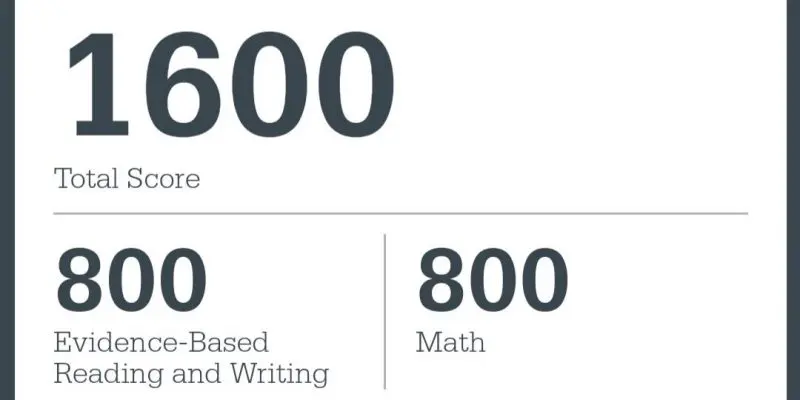
Turn SAT Pressure Into a Full Score
Looking for reliable SAT assistance but afraid of falling into a scam?
This article pulls back the curtain on the methodology behind SAT workarounds.
Drawing from a decade of industry expertise, ELPIS combines the evolution of the SAT to reveal the “insider secrets” that the College Board hides from the public. We provide a comprehensive breakdown of every SAT cheating method currently on the market, to show you exactly how they work—and their real-world success rates.
We may not guarantee you’ll pick us to be your SAT cheating service provider, but we are 100% sure you won’t get burned by a scam after reading this guide.
Ready for a score that opens every Ivy League door?
An Overview of SAT Cheating History and Techniques
Using Bootlegged "Screenshot-to-Al" Tools
Using Remote Control Software
A Short Assessment of Bluebook’s Security Features
We have completely deconstructed Bluebooks architecture, and stay ahead of every update via deep-level reverse engineering.
Bluebook is an Electron-based application. While its visible interface relies on heavily obfuscated JavaScript tucked away in the app.asar archive, the real “teeth” of its security infrastructure don’t live there permanently. In a sophisticated cat-and-mouse move, Bluebook dynamically downloads its core security modules only when the test session begins and wipes them from the disk the moment it ends. We’ve bypassed this “self-destruct” mechanism to analyze these C++ native modules (.node), which bridge the gap between simple web code and low-level system control.
Key Security Features (Powered by C++ Native Hooks):
Hard Desktop Lockdown
It doesn't just "cover" your screen; it takes exclusive control of the desktop, rendering Alt-Tab, task switching, and secondary monitors useless.
Hotkey & OS-Level Suppression
By hooking into the Windows API, it silences critical shortcuts like Ctrl+Alt+Delete and PrintScreen. It essentially "blinds" the operating system's standard management tools.
Process Sniffing & Enumeration
It continuously scans the system's process tree. Any blacklisted signaturefrom remote desktops to packet sniffers-is flagged and reported instantly.
Network Scrutiny & Traffic Analysis
It monitors the computer's socket connections. If it detects any unauthorized data exfiltration or "tunneling" attempts, the exam is terminated.
Anti-Virtualization Detection
It queries hardware IDs and driver signatures to ensure it isn't being "sandboxed" inside a Virtual Machine like VMware or VirtualBox.
HID Input Filtering
It distinguishes between a physical USB keyboard/mouse and "synthetic" inputs. This effectively neutralizes remote control software by blocking all non-native input events.
Furthermore, Bluebook has weaponized the Sentry SDK. Originally an open-source tool meant for crash reporting and stability, it has been repurposed into a powerful telemetry snitch. It doesn’t just report crashes; it provides a granular, chronological log of your entire system state—processes, network spikes, and hardware changes—directly to the College Board’s servers.
Beyond software, you face Physical Network Bans. Many test centers—often local high schools—implement “Router Whitelisting.” Their firewalls are configured to kill any connection that isn’t headed straight to a verified College Board endpoint. When the hardware itself severs your lifeline, software-based “hacks” are dead on arrival.
How We Secure Your SAT Success:
A Deep-Kernel Approach
We deploy a state-of-the-art, Ring 0-level rootkit that operates with the highest system privileges. By interacting directly with the hardware, it extracts frame data from the staging buffers to reconstruct the screen image in real-time. Leveraging a Windows 0-day exploit, our payload functions within the Kernel space, achieving a “ghost” state: no active processes, no background services, no detectable fluctuations in network traffic, and zero application-layer TCP/UDP packet signatures. Neither the native Task Manager nor any third-party telemetry can collect a single byte of data regarding its existence. This ensures that your scores remain bulletproof, regardless of when or how the College Board conducts its audits.
Crucially, we do not follow the path of amateur “script kiddies” who attempt to blind, tamper with, or paralyze the Bluebook software. Instead, we compromise the Windows Operating System itself. As far as Bluebook is concerned, every security component is functioning perfectly, and the environment is pristine. Much like the famous “Brain-in-a-vat” thought experiment, we create a simulated “perfect world” for Bluebook to reside in.
By not interfering with the proctoring software’s functions, we achieve total invisibility. More importantly, this method is future-proof. Regardless of how Bluebook updates, it must still rely on the OS to execute—and we control the OS. Even if a future Windows update patches a specific vulnerability, we maintain our edge by deploying fresh 0-days or utilizing specific OS versioning strategies.
Admittedly, no malware is theoretically undetectable. However, the technical expertise, manpower, and time required to find us far exceed the capabilities of any exam provider. For instance, an effective—albeit extreme—method would be a Cold Boot Attack. A proctor would have to physically rip the RAM modules out of your machine mid-exam, flash-freeze them in liquid nitrogen to prevent data decay, and transport them to a forensics lab for bit-level analysis.
Such countermeasures are, quite simply, physically and logistically impossible.
Finally, for test centers equipped with hardware-level network jamming, we provide custom-engineered laptops designed to bypass physical network restrictions and ensure a stable connection under any conditions.

